EKS Implementation Steps
Posted on July 13, 2024
Different ways to approach
1. AWS Mnagement Console
2. Eksctl utility by AWS
3. Iac (Terraform, Ansible)
Prerequisites
1. AWS account with admin privileges
2. AWS CLI access to use kubernetis utility
3. Instance to manage cluster by kubectl
Step by Step method to create the cluster
1. Signin in your account
a. Visit: https://aws.amazon.com
b. Sign in with your credentials.
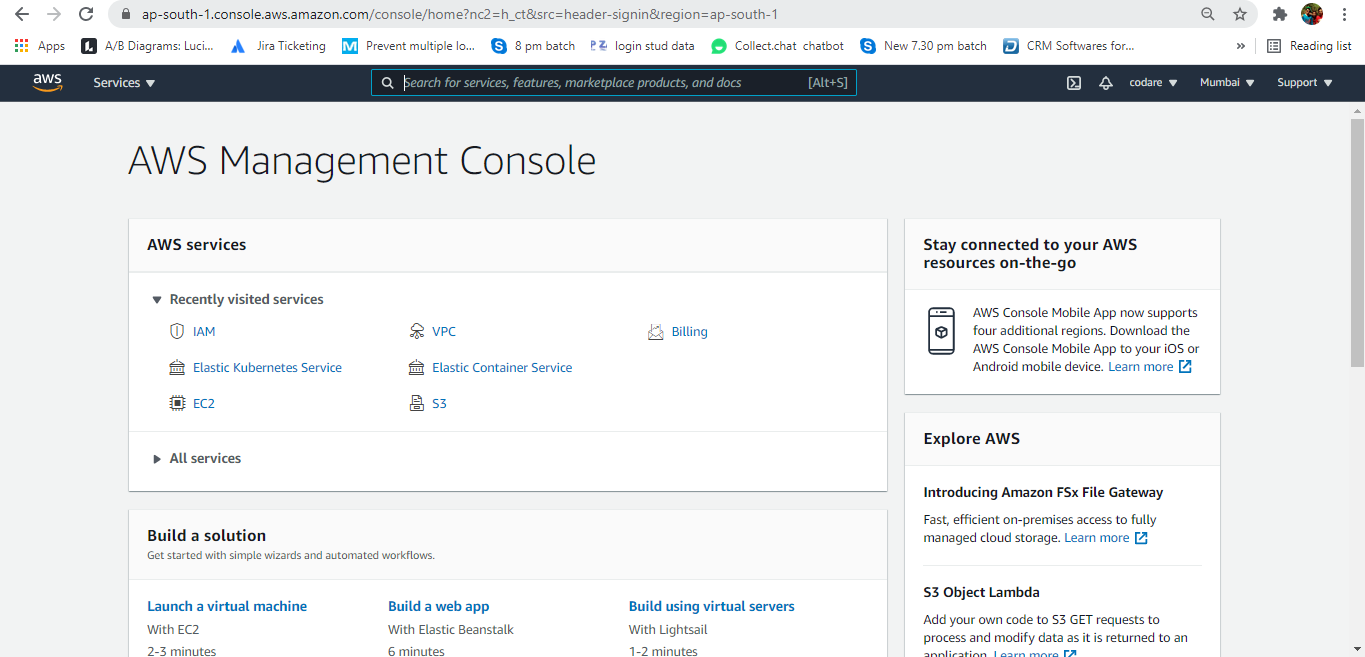
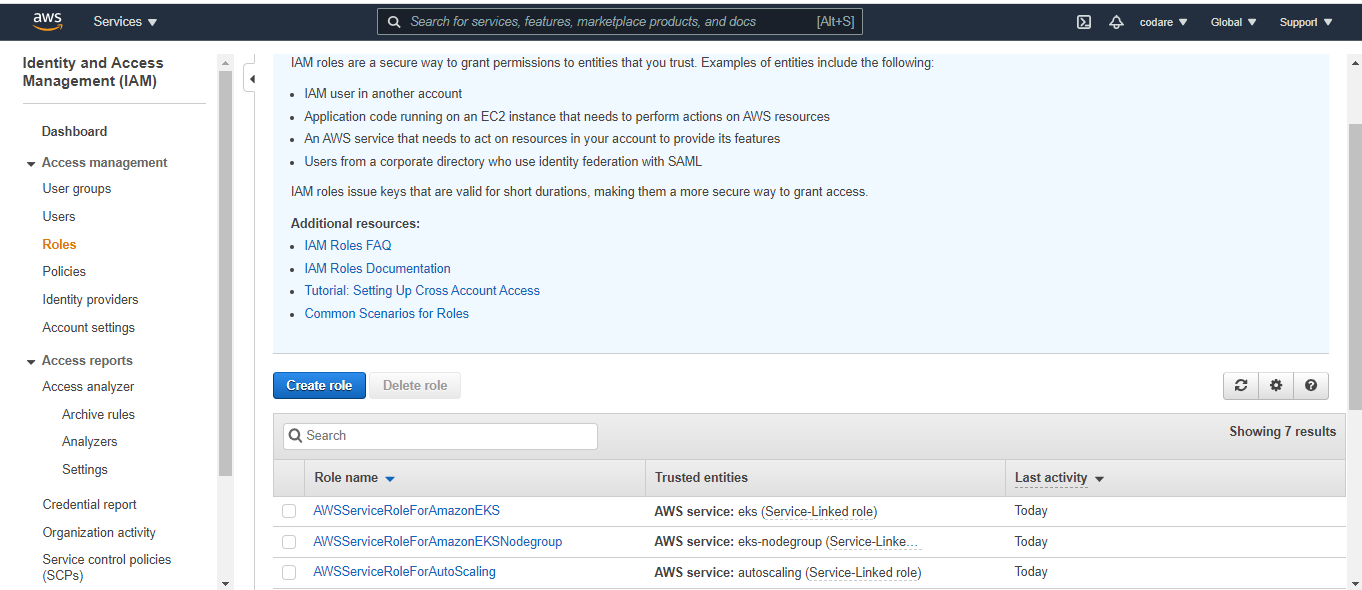
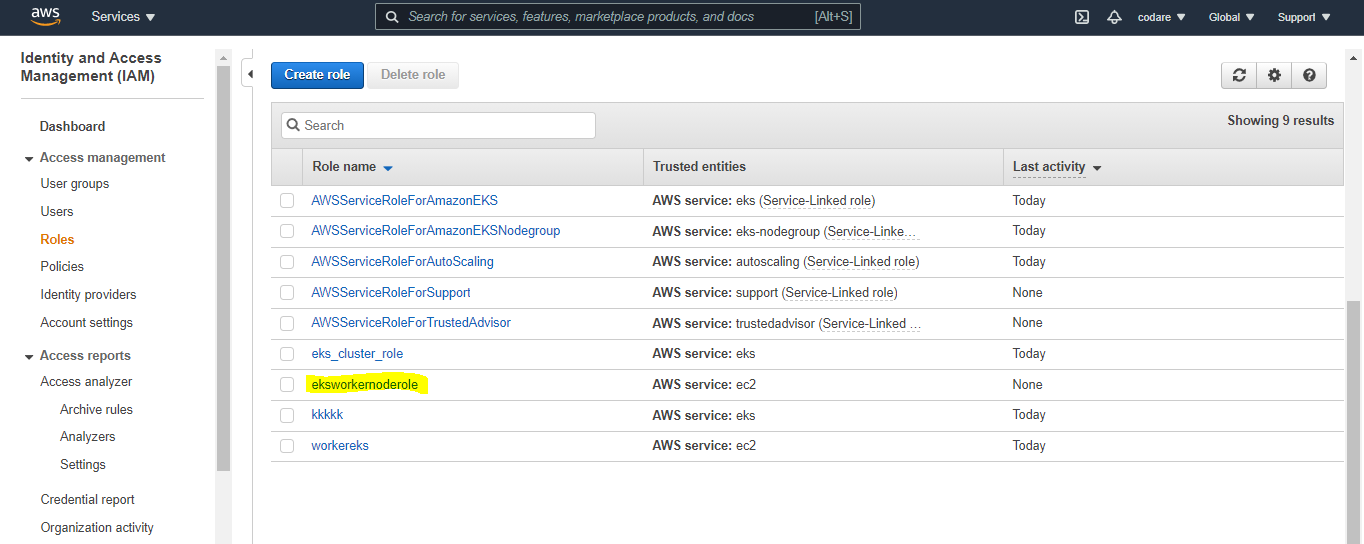
a. Click on services on the top left hand side and click on IAM
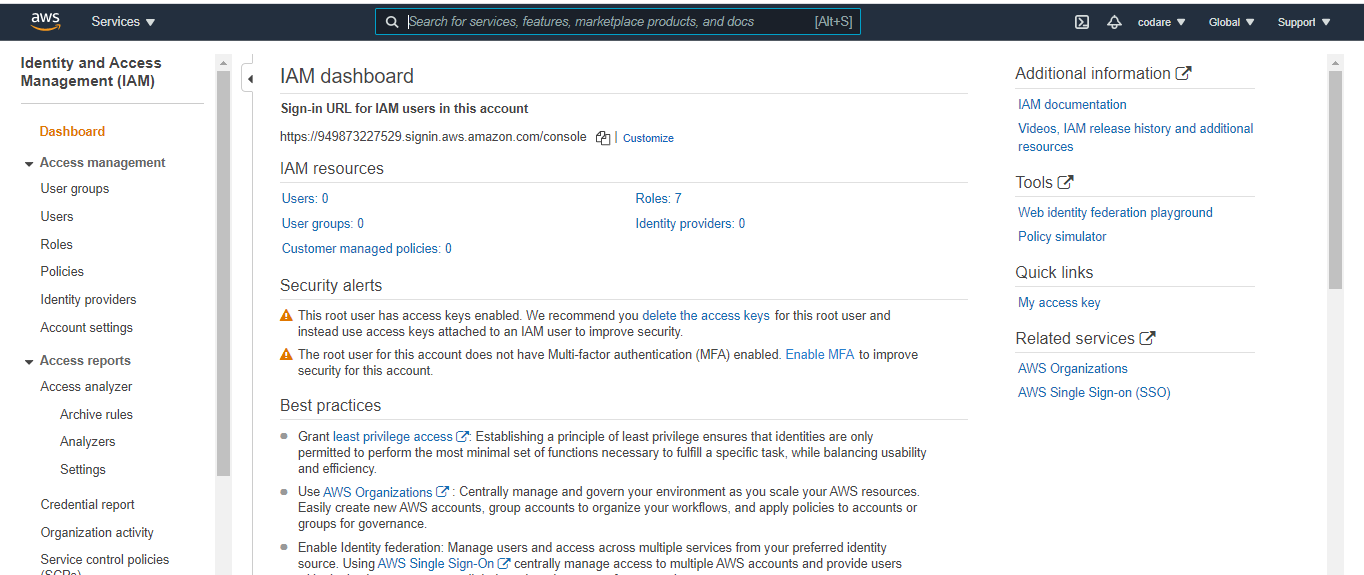
b. Go to Roles on left hand side.
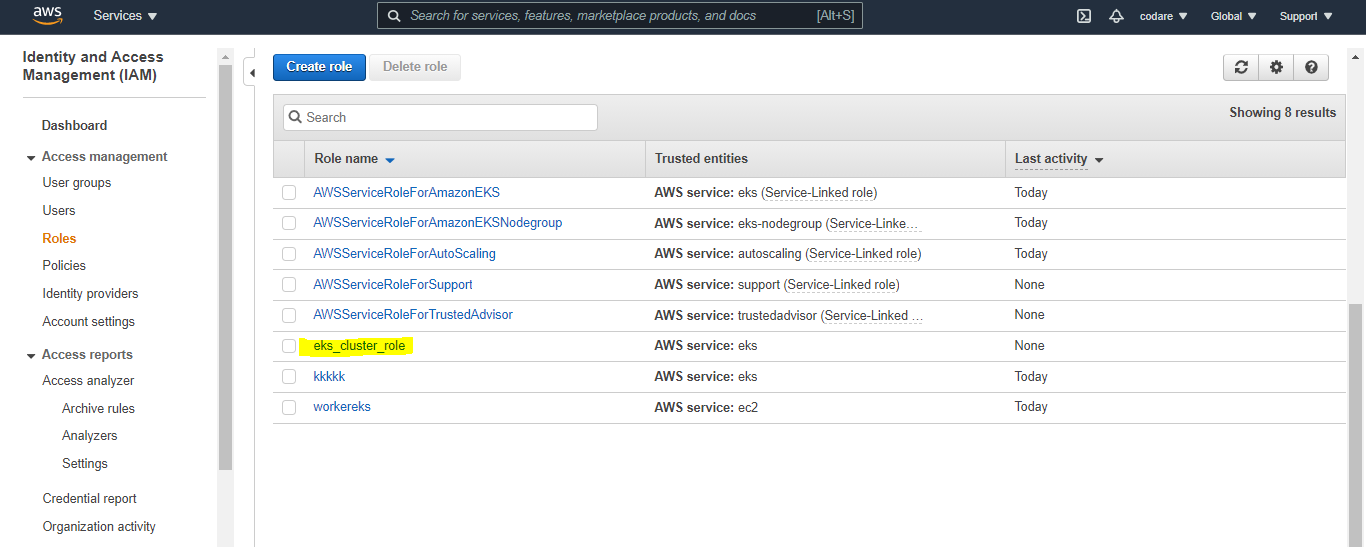
6. And write role name like eks_cluster_role and description is optional
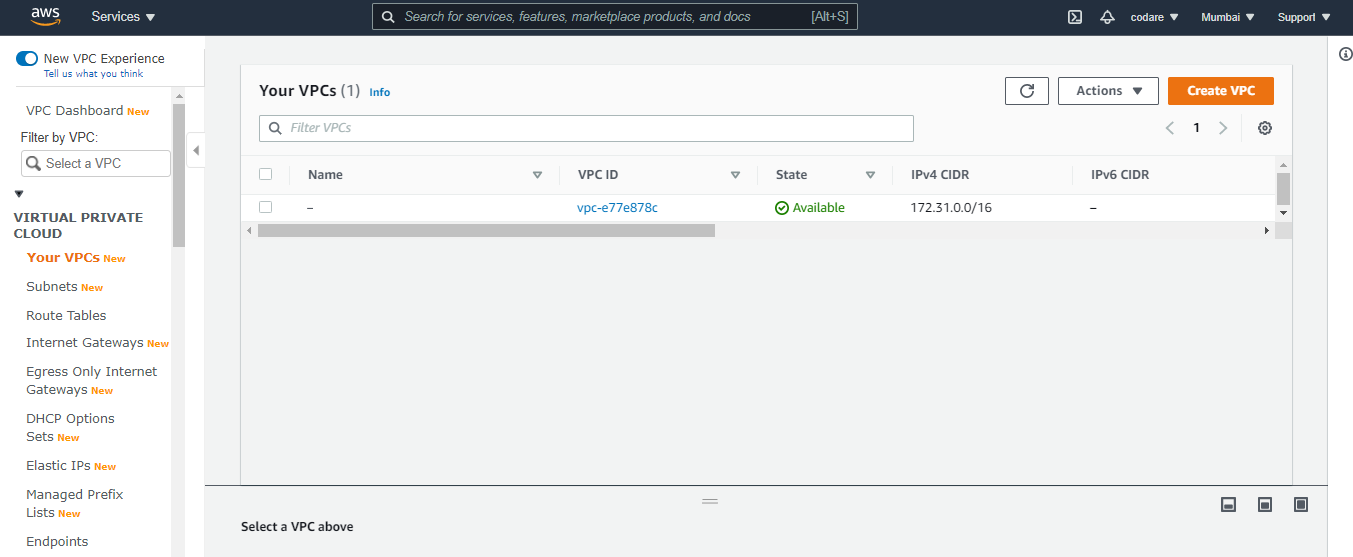
b. You can the the one that was default VPC
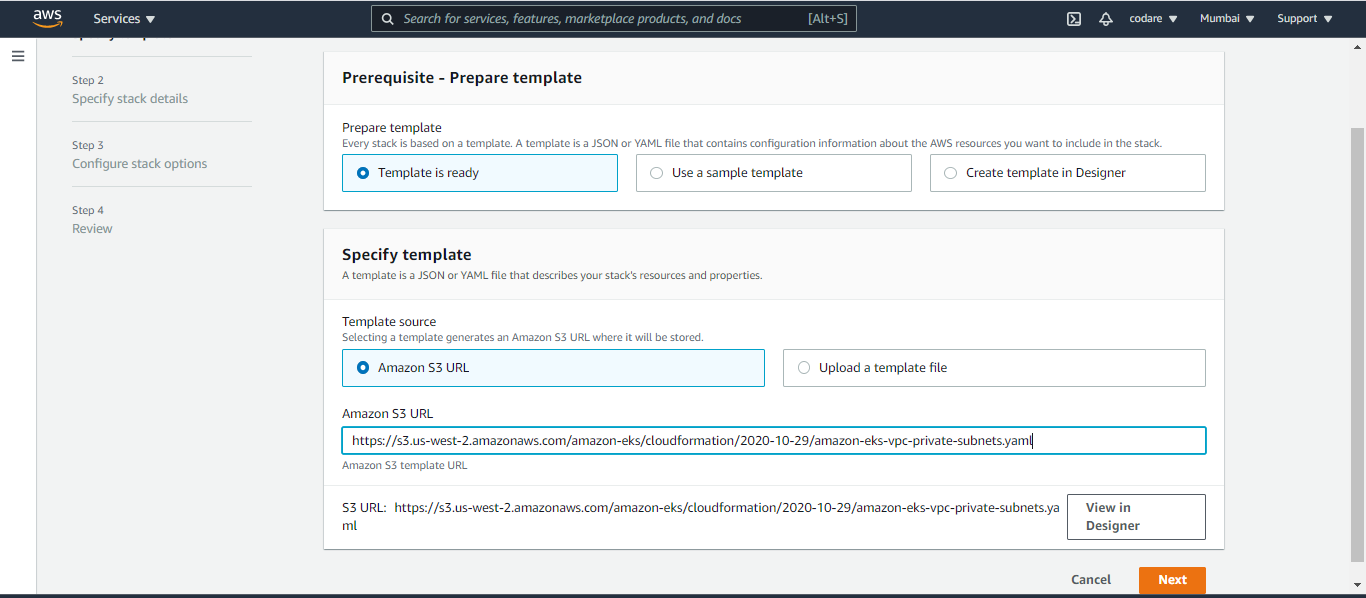
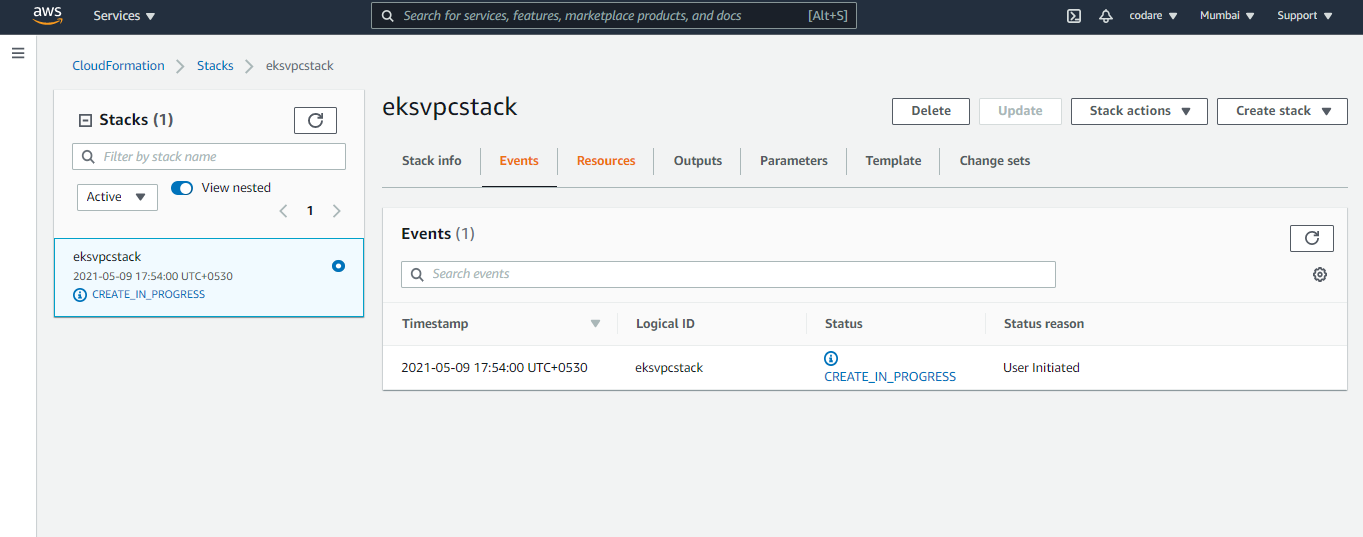
1. Click on Services and click on cloud formation
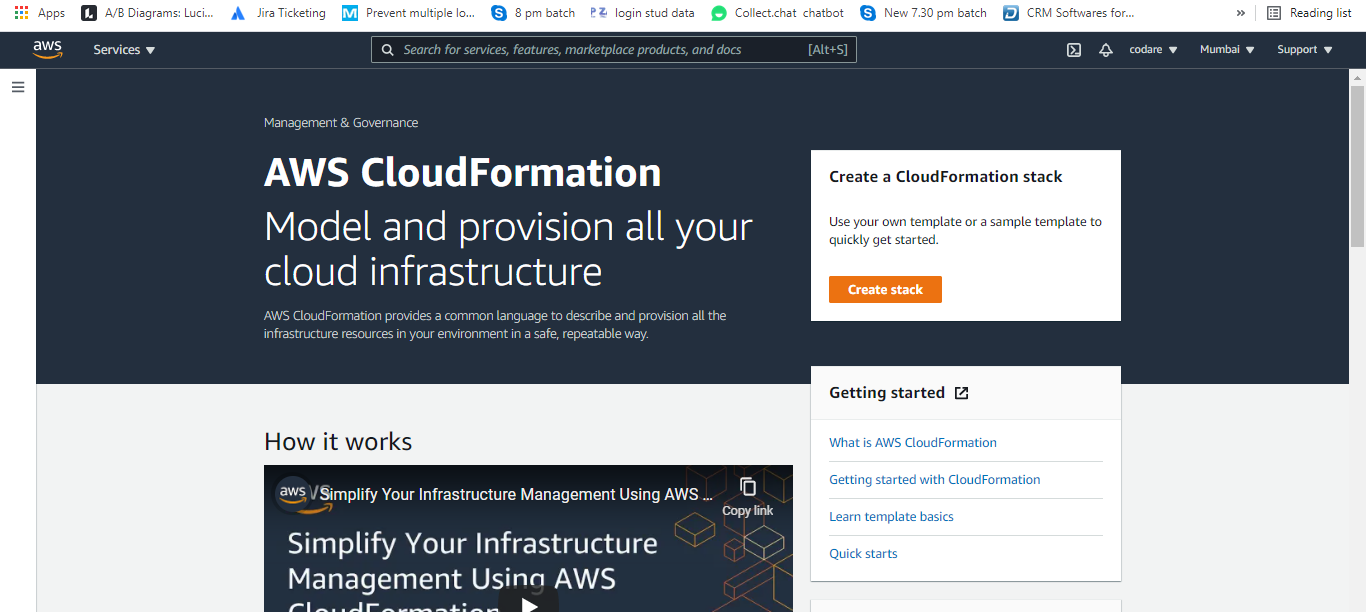
a. Then Click on Create Stack and Prepare template is (Template is Ready) and Specify template is choose Amazon s3 URL and write this url below https://s3.us-west-2.amazonaws.com/amazon-eks/cloudformation/2020-10-29/amazon-eks-vpc-private-subnets.yaml then click on next
c. Below the stack is creating and it take time after that verify our NAT and all vpc services from VPC which is created by stack and proceed next once stack is created.
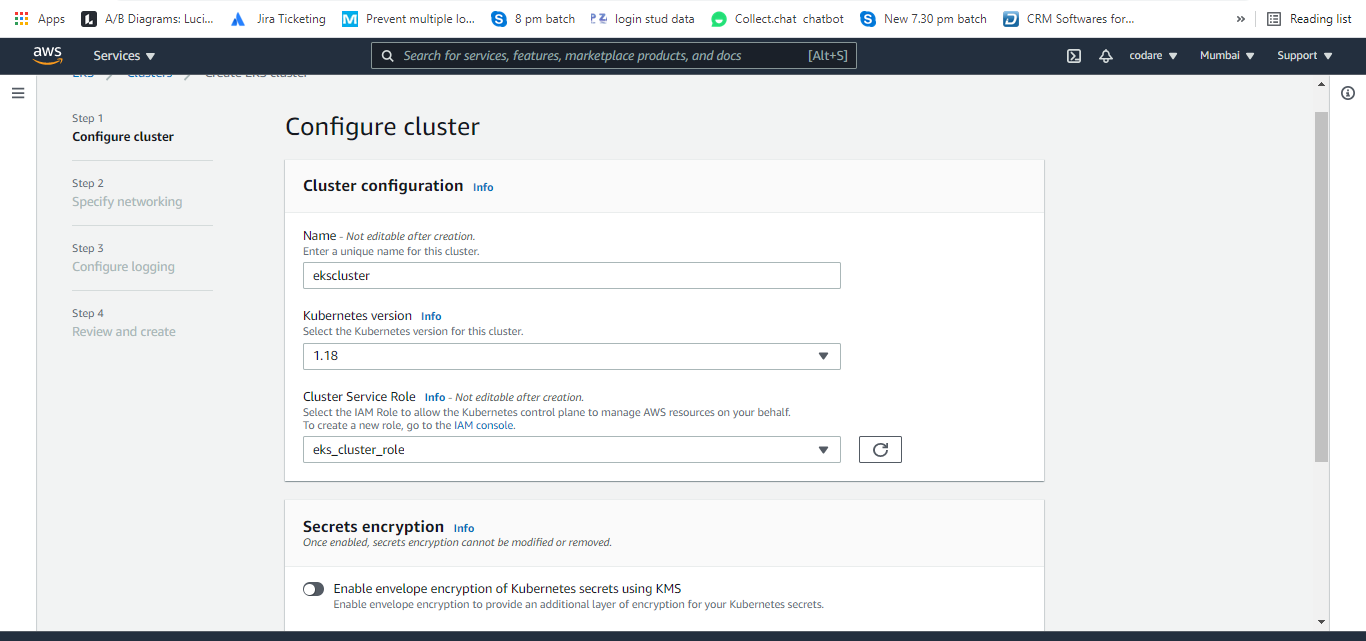
a. Select EKS from services and provide the name like ekscluster, provide the kubernetis version and select our existing created role eks_cluster_role.
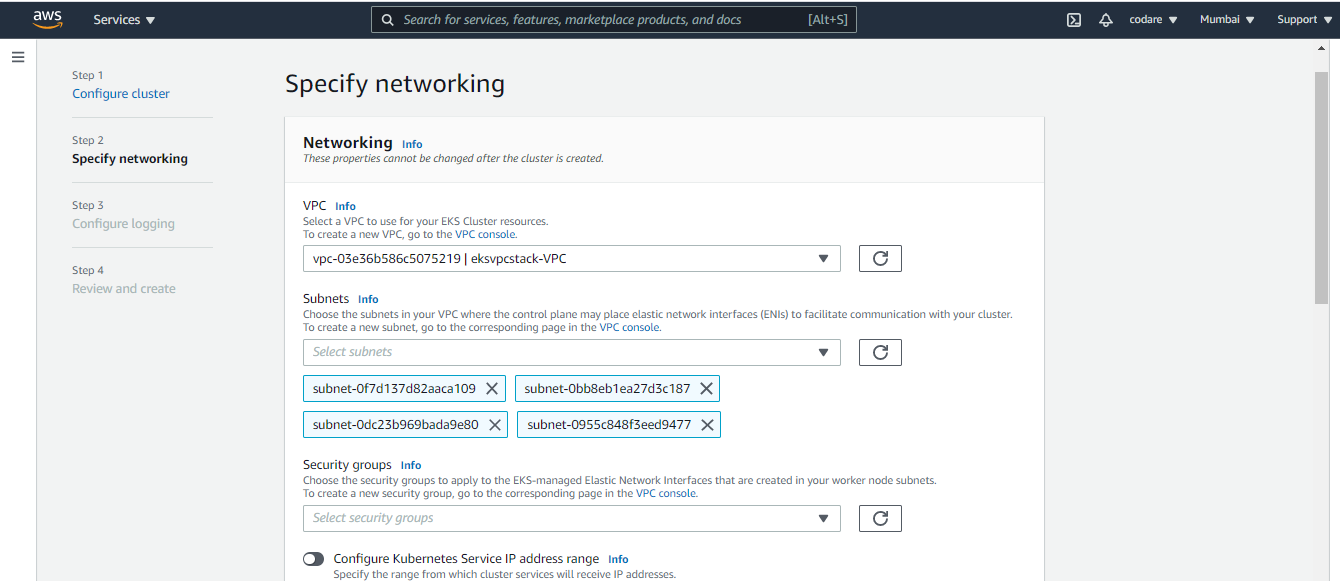
b. Click on the next and choose our early created VPC (created from cloudformation. You can see the name like eksvpcstack-VPC) and choose proper security group eksvpc security group which was created earlier and then select your network public, private or public and private (I choose public and private)
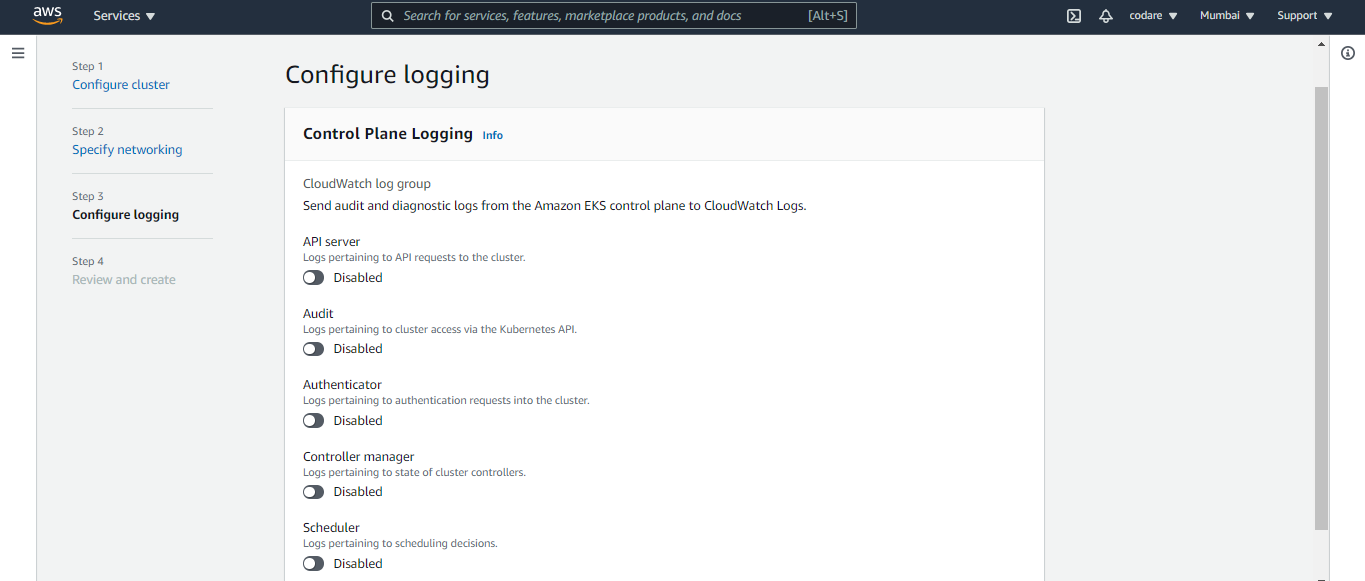
c. You can see Configure Logging . Control plane logging so enable the required parameters for test i am not enable anything and click on next and finally create the cluster. Image shown below for Configure Logging and wait for till the Cluster will create.
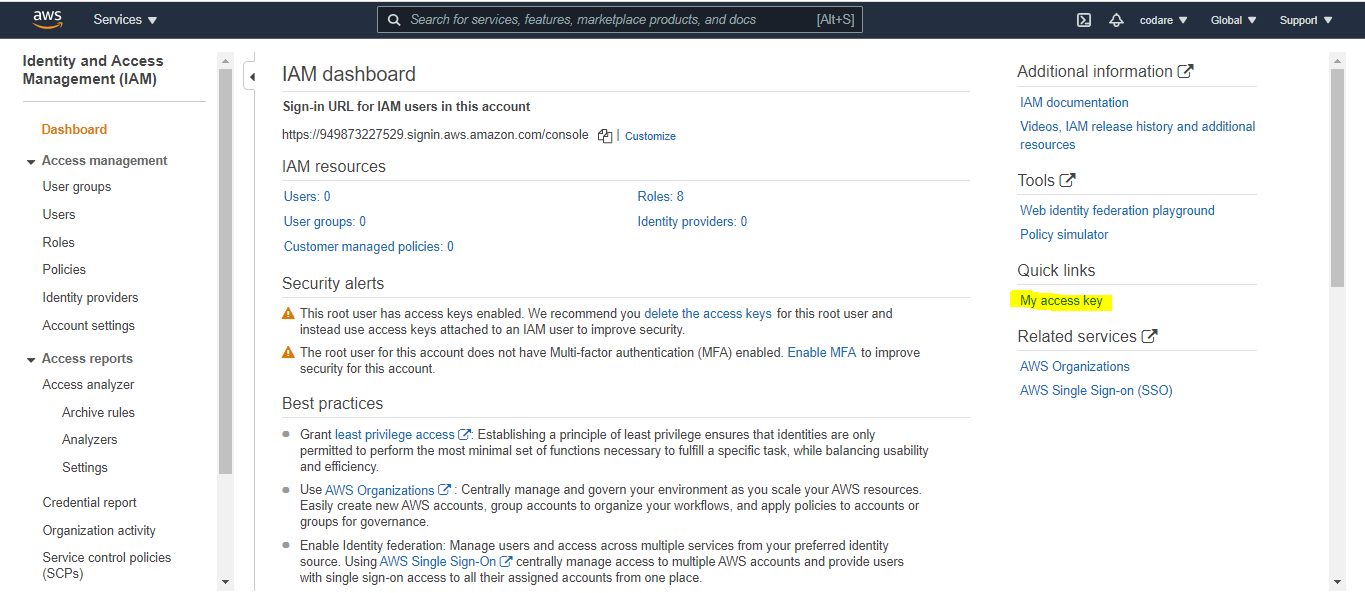
a. We need one instance to configure IAM authenticator and Kubectl utility to manage the worker node. So deploy one instance and as root in that instance follow the steps to configure the above one. So first to setup aws cli on that instance. The below Aws access and secret key will generate from IAM . See the below Image and create it
$ curl "https://s3.amazonaws.com/aws-cli/awscli-bundle.zip" -o "awscli-bundle.zip"
$ unzip awscli-bundle.zip
$ sudo ./awscli-bundle/install -i /usr/local/aws -b /usr/local/bin/aws
Add your Access Key ID and Secret Access Key to ~/.aws/config using this format:
$ aws configure
then fill your secret and access keys
[default]aws_access_key_id = enter_your_keyaws_secret_access_key = enter_your_keyregion = your region Protect the config file:
Optionally, you can set an environment variable pointing to the config file. This is especially important if you want to keep it in a non-standard location. For future convenience, also add this line to your ~/.bashrc file:
export AWS_CONFIG_FILE=$HOME/.aws/configThat should be it. Try out the following from your command prompt and if you have any s3 buckets you should see them listed:
aws s3 lsaws [options and parameters*]
a. Once the Instance is ready then check any aws command. In my case I am checking aws iam list-user
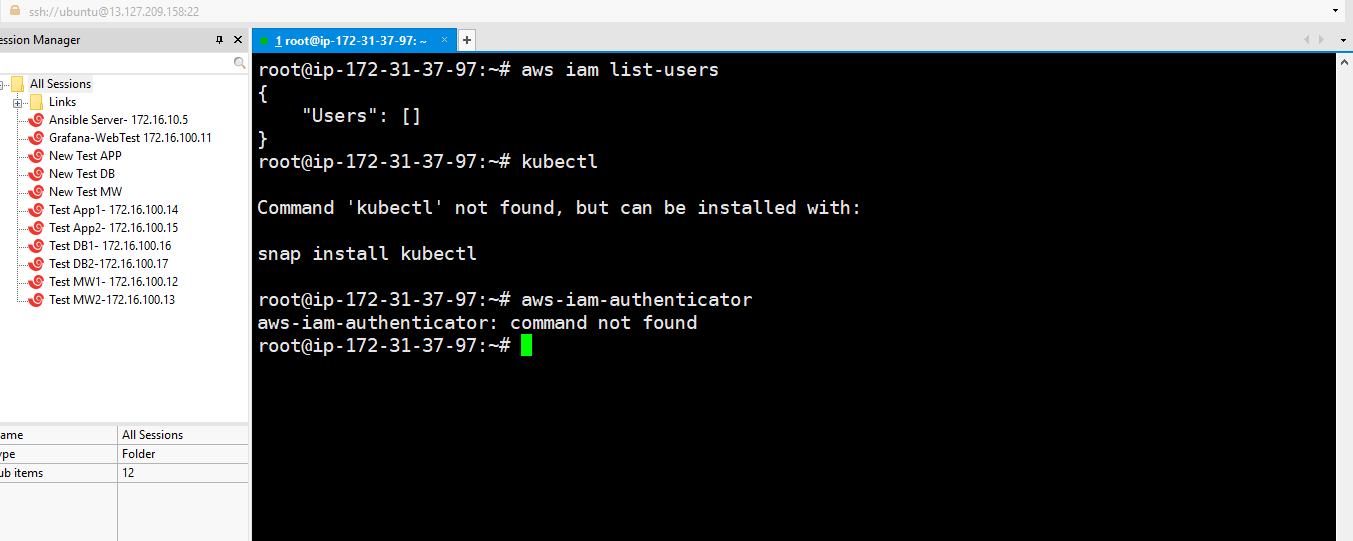
***********Aws-iam authenticator steps (for linux in my case)**********
$ curl -o aws-iam-authenticator https://amazon-eks.s3.us-west-2.amazonaws.com/1.19.6/2021-01-05/bin/linux/amd64/aws-iam-authenticator$ curl -o aws-iam-authenticator.sha256 https://amazon-eks.s3.us-west-2.amazonaws.com/1.19.6/2021-01-05/bin/linux/amd64/aws-iam-authenticator.sha256$ openssl sha1 -sha256 aws-iam-authenticator$ curl -o kubectl https://amazon-eks.s3.us-west-2.amazonaws.com/1.19.6/2021-01-05/bin/linux/amd64/kubectlc. $ kubectl get svc (check our Control SVC but not work here says connection refused)d. $ aws eks --region ap-south-1 update-kubeconfig --name ekscluster (local kubeconfig configuration set )e. $ export KUBECONFIG=~/.kube/configf. $ kubectl get svc (this command work here)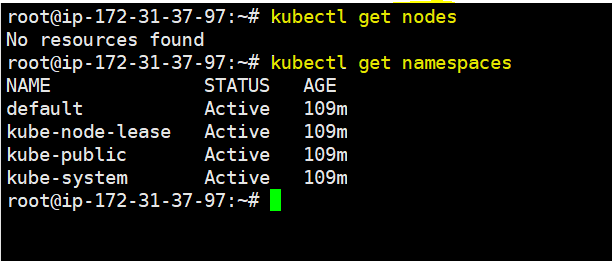
g.
$ kubectl get nodes and $kubectl get namespace (otutput shown below)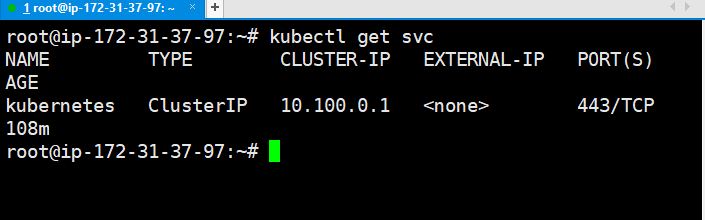
c. Click next, Tags are optional and Again next and enter the name of the role in my case name is eksworkernoderole and then create the role.
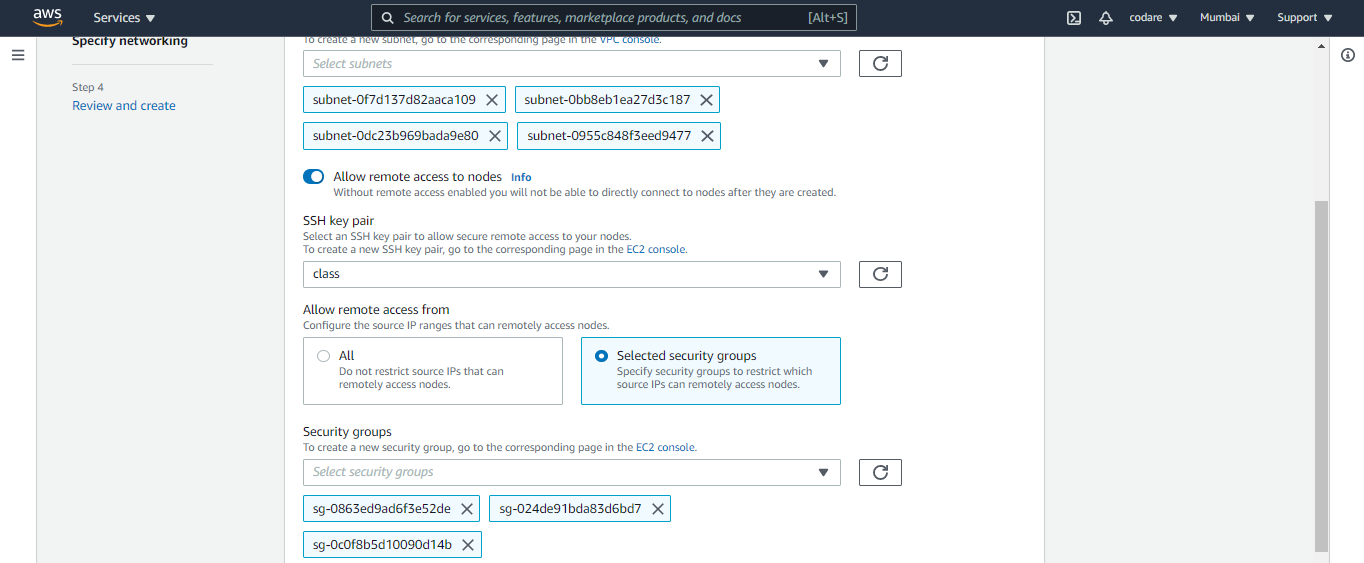
g. Then specify network fields , then select the fields below shown in diagram then next and click on create. (Please create your ssh keys first)
h. Then wait for Active the state after that just fire the $ kubectl get nodes and you can see the 2 worker nodes as I mention size 2 in above step.
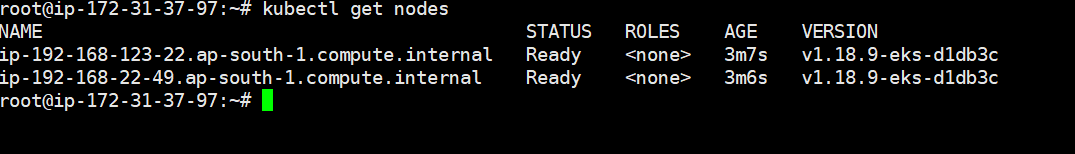
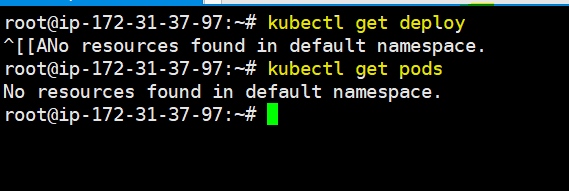
i. Now check pods and deploy to check is there any pods or deployment are there. But this is fresh new setup so no pods and no deploy. Please see below
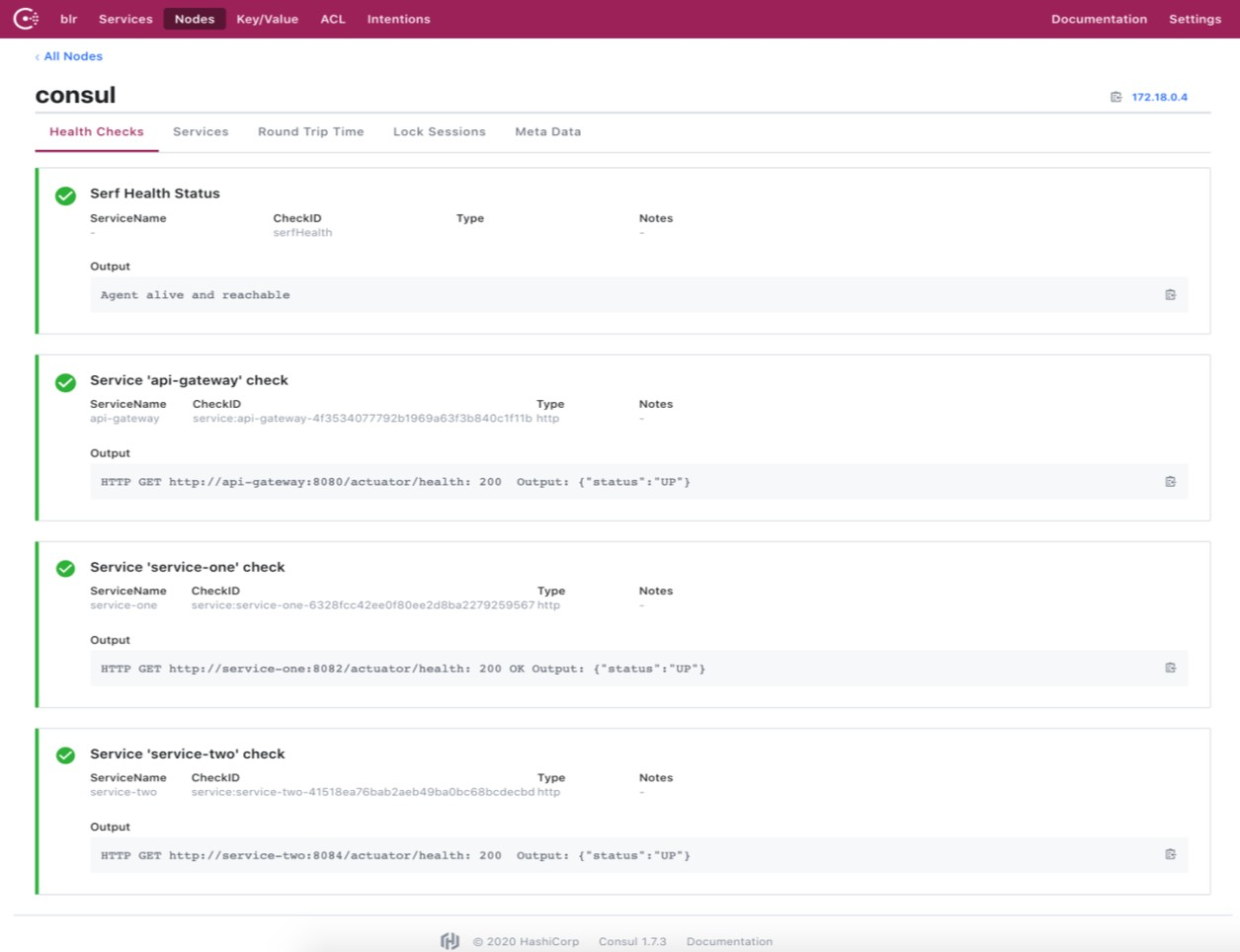
$ git clone https://github.com/vmudigal/microservices-sample.git$ cd microservices-sample$ mkdir yamls$ cd yamls$ kubectl apply -f xyz.yaml (here apply one by one all the yamls ) $ kubectl get svcConsul Management console: http://awslink:8500/ui/
Tools: Weavescope Management Console: http://awslink:4040/
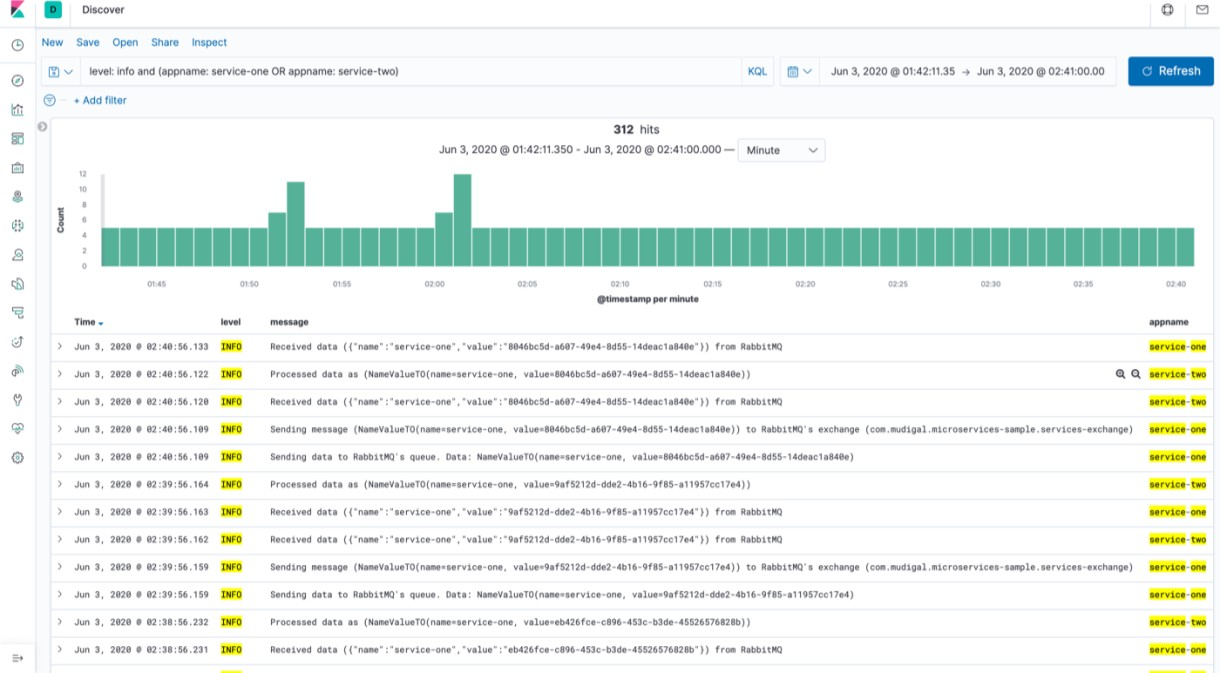
CENTRALIZED LOGGING USING ELK
http://awslink:5601/app/kibana
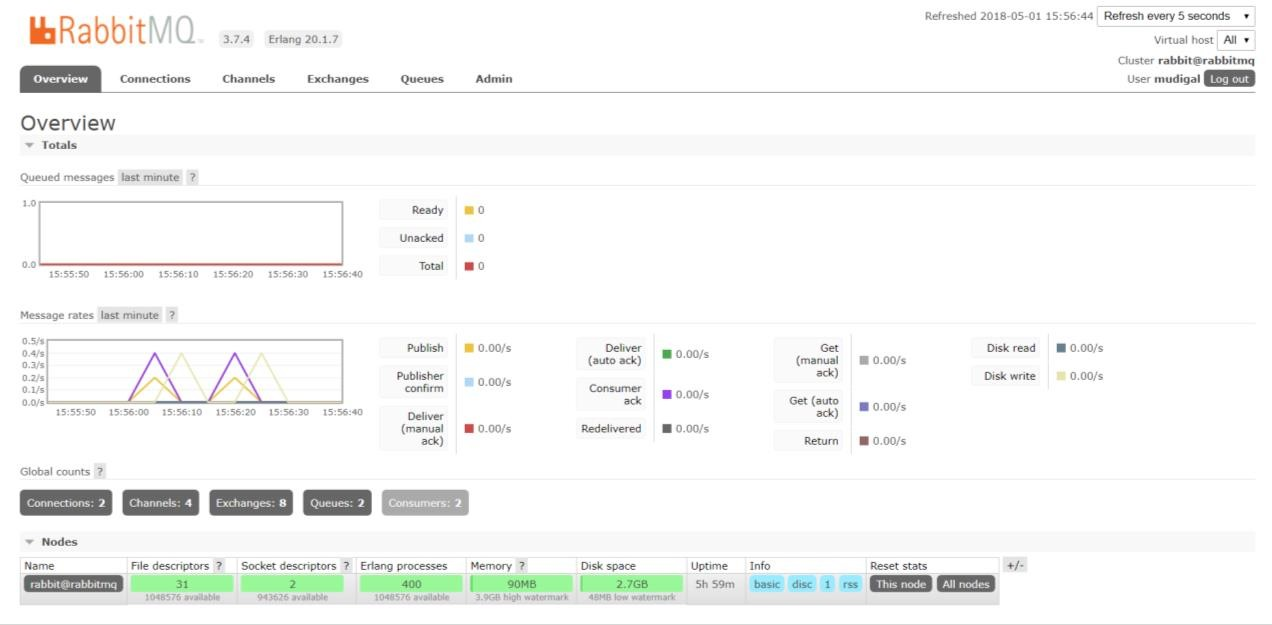
Tools: RabbitMQ Management Console: http://awslink:15672/